Security is a major concern for every organization. But when it comes to UC security many organizations are less concerned .
Some major changes happened with UCM security . Today’s blogs is all about comparing the UCM security and the changes with different CSR revision.
We all are familiar with UCM Non Secure and Mixed mode. I am not explaining the process of converting non secure to mixed mode. Because on google you can find large number of documents regarding this.
CUCM provides two security modes:
- Non-secure mode (default mode)
- Mixed mode (secure mode)
Non-secure mode is the default mode when a CUCM cluster (or server) is installed fresh. In this mode, CUCM cannot provide secure signaling or media services. With Mixed mode you can have secure signalling and media service.
Do we need Mixed mode to make signaling and media encrypted ? NO, With the latest version we don’t need mixed mode to encrypt the signaling and media.
Cluster Security Mode: Feature Tradeoffs
BEFORE CSR 12.0
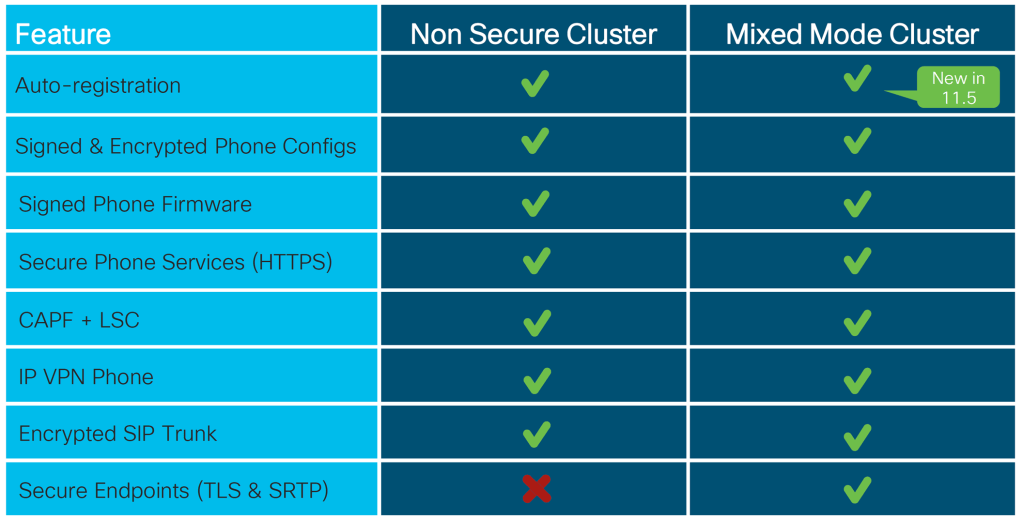
API Protection
*: Requires CAPF enrollment and “mixed mode”
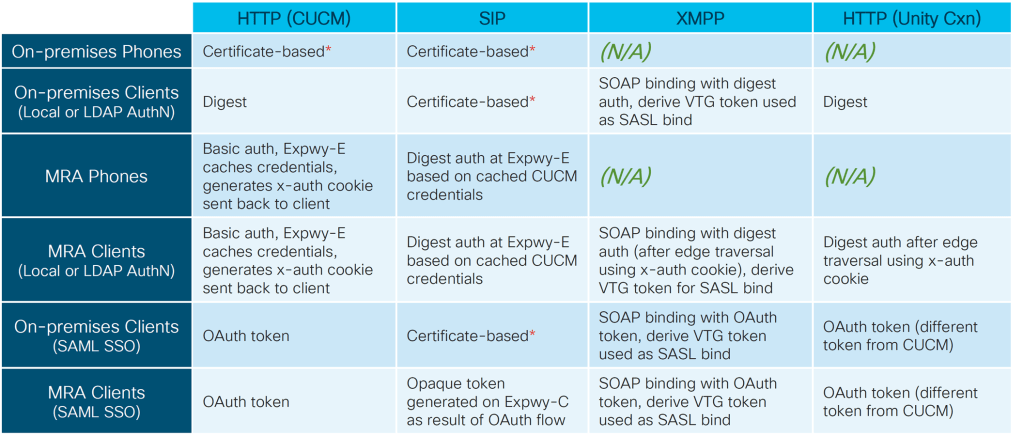
CSR 12.5
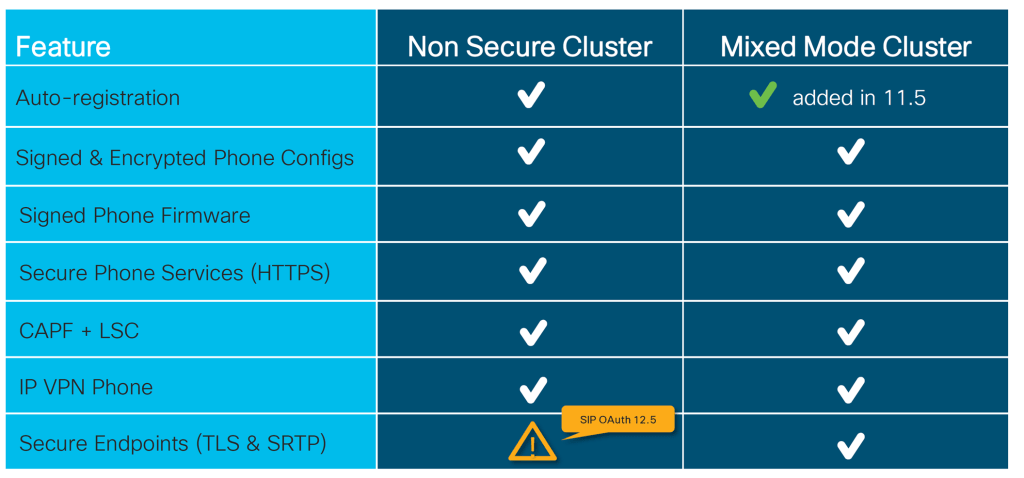
SIP OAuth for Jabber on Non Secure cluster.
API Protection
*: Requires CAPF enrollment and “mixed mode”
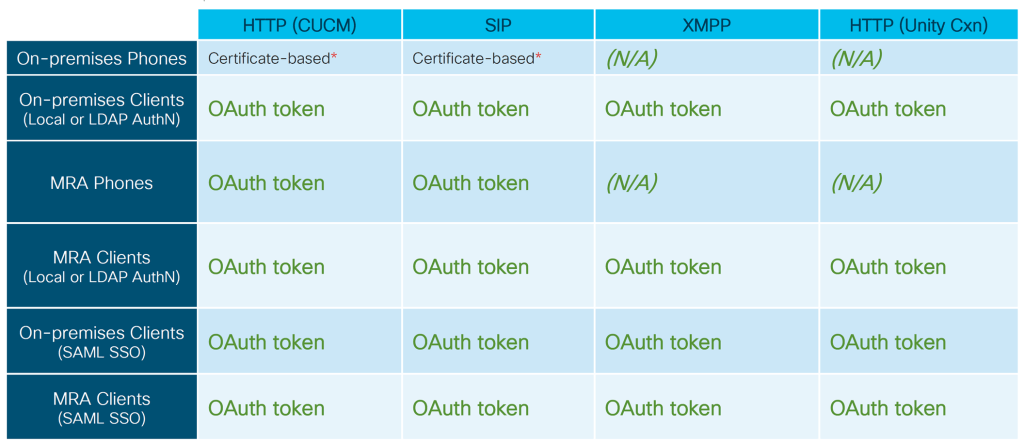
CSR 14

API Protection
No need for CAPF enrollment or “mixed mode”
SIP OAuth Mode Overview
Secure registrations to Unified Communications Manager involves a process of updating CTL files, setting up a mutual certificate trust store and so on. If devices are switching between on-premises and off-premises, it is difficult to update LSCs and renew Certificate Authority Proxy Function (CAPF) enrolment each time when a secure registration is completed.
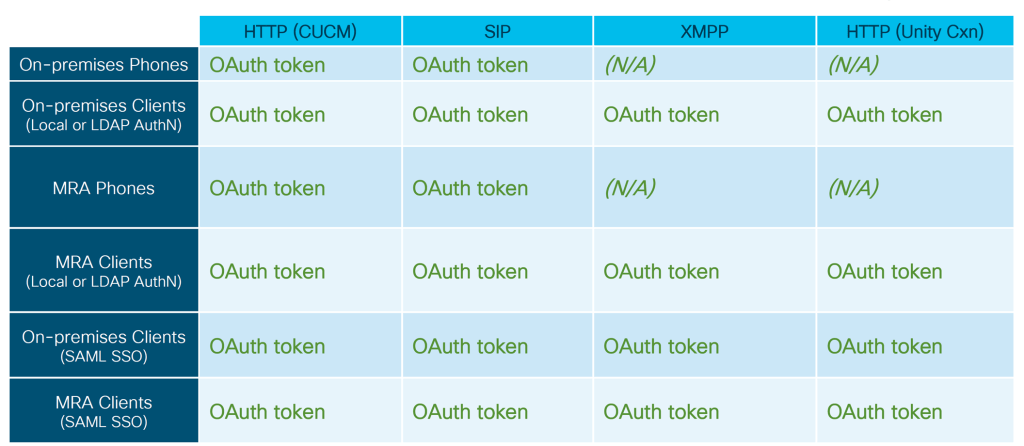
SIP OAuth mode allows you to use OAuth refresh tokens for all devices authentication in secure environments. This feature enhances the security ofUnified Communications Manager.
Unified Communications Manager verifies the token presented by the endpoints and serves the configuration files only to authorized ones. OAuth token validation during SIP registration is completed when OAuth based authorization is enabled on Unified Communications Manager cluster and other Cisco devices.
OAuth support for SIP registrations is extended for
- Cisco Jabber devices from Cisco Unified Communications Manager 12.5 release onwards
- SIP Phones from Cisco Unified Communications ManagerRelease 14 onwards
The following are the Phone Security Profile Types that can be configured for OAuth.
- Cisco Dual Mode For iPhone (TCT device)
- Cisco Dual Mode For Android (BOT device)
- Cisco Unified Client Service Framework (CSF device)
- Cisco Jabber for Tablet (TAB device)
- Universal Device Template
- Cisco 8811
- Cisco 8841
- Cisco 8851
- Cisco 8851NR
- Cisco 8861
- Cisco 7811
- Cisco 7821
- Cisco 7841
- Cisco 7861
- Cisco 8845
- Cisco 8865
- Cisco 8865NR
- Cisco 7832
- Cisco 8832
- Cisco 8832NR
Before deciding to go with OAuth, make sure you met all requirement.
SIP OAuth Mode Prerequisites
This feature assumes that you have already completed the following:
- Ensure Unified Communications Manager is registered to a Smart or Virtual account with allow export-controlled functionality.
- Ensure client firmware supports SIP OAuth.
SIP OAuth Mode Configuration Task Flow
Complete the following tasks to configure SIP OAuth for your system.
Procedure
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | Upload CA Certificate to the Phone Edge Trust | Upload CA Certificate to the phone edge trust to get the tokens. This step is not applicable for Cisco Jabber device. |
| Step 2 | Enable OAuth Access Token for Devices | Enable OAuth for SIP registrations in Cisco IP Phone 7800 and 8800 enterprise series. This step is not applicable for Cisco Jabber device. |
| Step 3 | Configure Refresh Logins | Enable oauth with refresh login flow on Unified Communications Manager to register the device via SIP OAuth. |
| Step 4 | Configure OAuth Ports | Assign the ports for OAuth for each node that has OAuth registration. |
| Step 5 | Configure OAuth Connection to Expressway-C | Configure a mutually authenticated TLS connection to Expressway-C. |
| Step 6 | Enable SIP OAuth Mode | Enable OAuth services using a CLI command on the publisher node. |
| Step 7 | Restart Cisco CallManager Service | Restart this service on all nodes that have OAuth registrations. |
| Step 8 | Configure Device Security Mode in Phone Security Profile | Configure OAuth support within a Phone Security Profile if you are deploying encryption for the endpoints. |
| Step 9 | (Optional) Configure SIP OAuth Registered Phones for MRA Mode | (Optional) Configure SIP OAuth registered phones in MRA mode. This step is not applicable for Cisco Jabber device. |